Introducing a hybrid approach to using Document AI and GenAI
Corporate Mobility, Taking Things Easy with BCR, and Pet Reptiles
August 20, 2018
August 20, 2018
Supercharge AI automation with the power of reliable, accurate OCR
Increase straight-through document processing with data-driven insights
Integrate reliable Document AI in your automation workflows with just a few lines of code
PROCESS UNDERSTANDING
PROCESS OPTIMIZATION
Purpose-built AI for limitless automation.
Kick-start your automation with pre-trained AI extraction models.
Meet our contributors, explore assets, and more.
BY INDUSTRY
BY BUSINESS PROCESS
BY TECHNOLOGY
Build
Integrate advanced text recognition capabilities into your applications and workflows via API.
AI-ready document data for context grounded GenAI output with RAG.
Explore purpose-built AI for Intelligent Automation.
Grow
Connect with peers and experienced OCR, IDP, and AI professionals.
A distinguished title awarded to developers who demonstrate exceptional expertise in ABBYY AI.
Explore
Insights
Implementation
People seem to be using their mobile everywhere, even in the workplace. Today we’ll tell how businesses can take advantage of mobile technology. Also tips on using the ABBYY BCR in advertising and measuring your Internet speed and exotic pets.
Almost all companies today use some sort of mobile or computer technology to optimize their business processes and improve efficiency. At the same time, almost every employee owns a smartphone, a tablet or a laptop. Those of them who have access to sensitive information, proprietary databases, and confidential documents pose a serious security risk, as the data they work with can be hijacked by fraudsters and become available to the competition. Naturally, information security is a top priority for company management and IT departments.

The obvious solution would seem to be to banish all personal mobile devices from the workplace. But the downsides to this approach are just as obvious. Firstly, banning smartphones would have an adverse effect on workforce loyalty, as many employees would see it as an encroachment on their personal freedoms. Secondly, working from home is a global trend. Many professionals no longer have to come to the office every day in order to do their job properly. Some of them don’t even need a permanent desk, saving their companies thousands on office leases.

There is a good solution, however, and it is called BYOD (Bring-Your-Own-Device). Companies with BOYD policies in place allow their employees to use their personal mobile devices for work. This means they are always connected and can do some or even all of their office assignments when they are away on business, working with customers on site, or just working from home.
The BYOD abbreviation came into common use at the beginning of the noughties, when smartphones and tablets started to infiltrate our daily lives.

The BYOD approach relies on EMM (Enterprise Mobility Management), a set of services and technologies designed to protect corporate intellectual property. EMM is not just a separate set of security measures but is tightly integrated with work processes and objectives, so that mobile security can be seamlessly enforced across all platforms and software without radically overhauling the existing IT infrastructure.

EMM is an umbrella term that covers many different mechanisms. Each company must select the EMM mechanism that best suits its needs after considering many different factors, such as:
Let’s take a closer look at some of the more common EMM components.
MDM (Mobile Device Management)
MDM lies at the heart of mobile security. It gives companies almost complete control over mobile hardware. Typically MDM involves installing a unique profile on a mobile device that is to be used as part of BOYD. This profile enables the company to set various restrictions for the device and encrypt its data. For example, the company’s IT engineers can erase all of the data from a BOYD device if it is lost or stolen. MDM tracks your phone status in real time, detects any changes to its OS, and even provides troubleshooting tools to address certain malfunctions. The company will also be able to track the location of your phone if you choose to use it for work.
MAM (Mobile Application Management)

This tool works directly with installed apps, allowing your IT department to download, install, and update apps on your phone remotely. Your system administrators will set up different access permissions for different apps and will be able to delete certain app data. MAM may be an optimal choice in many cases, because it does not give companies full control over their employees’ phones, but only over some of the apps that access sensitive data.
MIM (Mobile Information Management)
MIM allows you to access your company’s databases from your mobile device over a secured connection. MIM is usually used in conjunction with MDM and MAM, because the latter two are typically integrated with cloud services and store and exchange large swathes of information in clouds. MIM supports popular cloud storage services, including Box, Dropbox, and Google Drive.
MCM (Mobile Content Management)

This is similar to MIM, but offers more powerful content management capabilities. MCM provides content access controls and secure file-level access to databases stored on mobile devices. MCM platforms also support many of the popular cloud storage services.
MEM (Mobile Expense Management)
MEM solutions enable companies to control expenses associated with the use of mobile devices by their employees. A MEM tool will gather statistics about data usage, calls, and messages. It is very much like a mobile auditor that keeps an eye over the employees’ mobile expenses.
Some companies will use only some of the above mechanisms and some will combine them to meet their business needs, depending on the sensitivity of their information, the number of employees, and some other factors. In this day and age information is king, so companies will readily invest into security solutions that will help protect their most valuable asset.

There are lots of different EMM solutions available on the market, such as MobileIron, Google G Suite, VMware AirWatch, Microsoft Intune, Citrix XenMobile, and Symantec Mobile Management. Few developers, however, will offer the complete range, so businesses often need to book multiple services in order to cover all the bases.
Sometimes a company may create a corporate app store where its employees can download and install apps that they need for their work. These are very much like the usual app stores, only with a limited range of apps and tight security mechanisms in place.
The screenshot below shows a corporate app store maintained by Aviadvigatel, developer of jet engines and gas turbines. Data security technologies for the store have been provided by the IT company Croc.
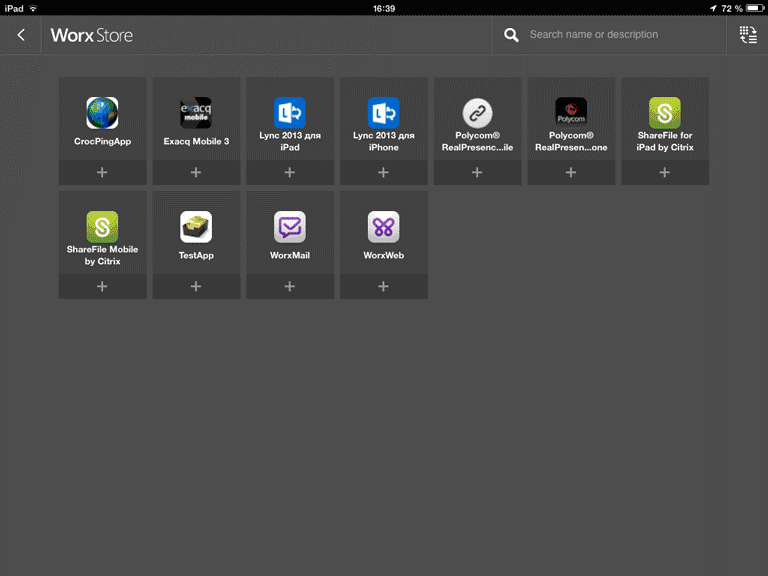
In companies like these, employees deal with highly sensitive information that costs millions, so they are only allowed to install apps vetted by their IT departments.
In the next screenshot, you can see the desktop of a corporate iPad displaying the apps that are used for work.

There are security tools available for the majority of popular mobile platforms, including iOS, Android, and Windows 10 Mobile. Similar solutions are also available for Mac OS and Windows.
A recent survey by Forrester Research involving 2114 international companies revealed that 77% of them are planning to continue to implement EMM solutions.
In the next issues we will talk more about the tools of corporate mobility and security.
Those who work in advertising need to interact with hundreds of business contacts, including suppliers, contractors, space providers, event managers, designers, and many more.
Here’s a picture of a business card book of an advertising manager. It currently holds more than 500 cards, almost all of which are in constant use.
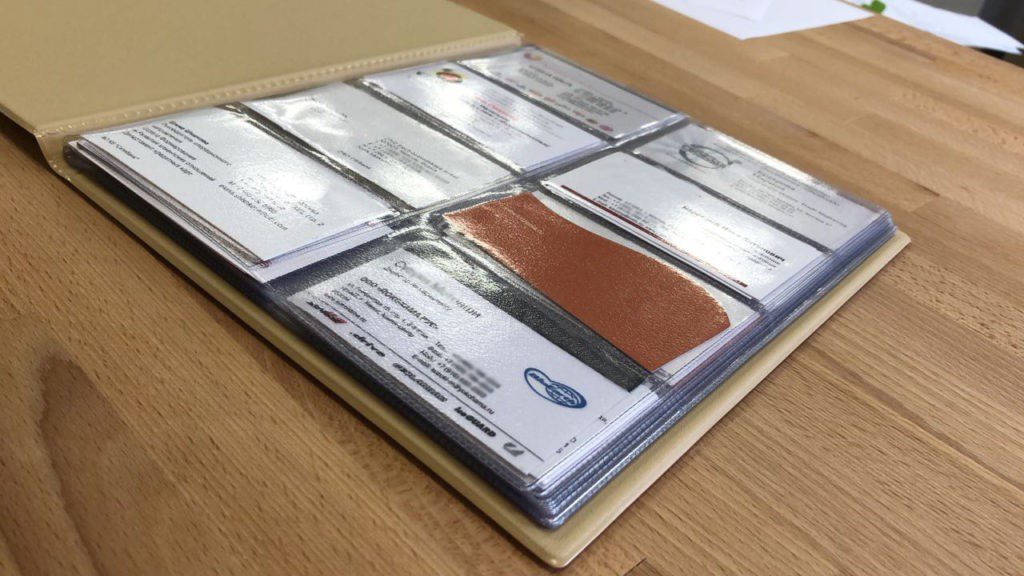
The owner has to thumb through this book carefully to find a contact. When she needs to share contacts with colleagues, they either take snapshots of the business cards they need or just borrow the paper originals, which can be easily lost.
To have your business contacts always to hand, you can digitize them using BCR, an app that captures business cards and stores them on your mobile device. Capturing cards with BCR is six times faster than typing the details manually. You can also instantly share your business cards with your colleagues, access your repository from iOS or Android devices or from a desktop computer, create Excel reports, and perform lots of other useful manipulations.
Our favourite app this week comes from Speedtest, probably the most popular resource for measuring the speed of your Internet connection.
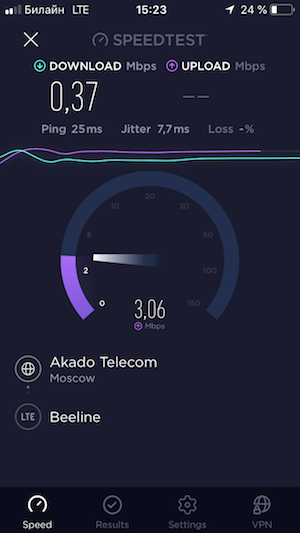
When you open the app on your device, you will see a large GO button. Tap it and wait a little while the app tests your connection. You will see both your current speed and a graph showing how the speed is changing during the measurement. The flatter the line, the more stable your connection.
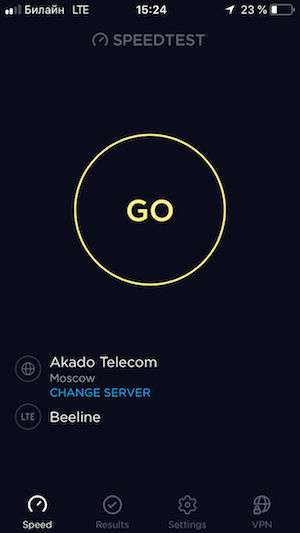
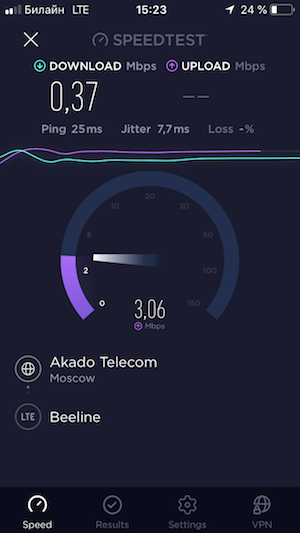
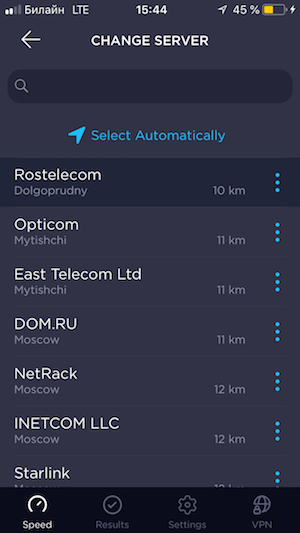
Should you want to double-check, you can change the remote server that is contacted by the app. Simply tap CHANGE SERVER on the main tab and you will see the available servers and how far they are from you.
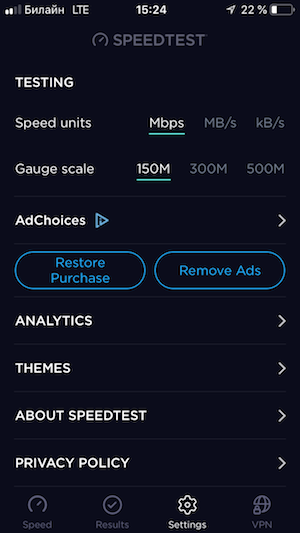
You can also change the speed units and the gauge scale.
The app will store your past measurements for reference. These can be found by tapping the Results tab at the bottom of the screen. History details include date and time, speed, and type of connection.
The Android version now allows you to check your mobile coverage (still in beta).


The app is available on iOS and Android.
By Milana Petruk, Webmaster

Choosing a scaly pet
If you want to have some wildlife in your home but don’t have the time to look after a feathered or furry creature, or if you are allergic to them, consider getting yourself a reptile.
There are lots of kinds of reptiles, some of which can be kept as pets. All reptiles have a life expectancy of over seven years and many will live to be 80 or even 100. Besides they can easily go without food for two or three days thanks to their slower metabolisms. First off, you will need to invest in a terrarium, i.e. a glass enclosure where you will keep your pet in optimal conditions. These usually come complete with a lid, heating lamps, ventilation, sand and other articles necessary to re-create its inhabitant’s natural environment. Be sure to buy a terrarium that fits the size and type of your future pet.
Here’s a checklist for your convenience:
Finally, remember that almost all reptiles are wild animals that won’t get attached to humans. They are more like gold fish than hamsters or gerbils. With that I mind, good luck and enjoy your new exotic pet when they arrive!
That’s all from us for today. See you next Monday.
P.S. You can find the previous issue of this newsletter here.